Vulnerability Scanning, The SEC, and You: The First Step in Securing your Network
Introduction
 In the last several years, the speak coming from regulators, customers, and vendors has all been centered on cybersecurity: what it is and how to have “good cybersecurity” or how to be “cybersecure”. By this point, we all realize that cybersecurity is not simply a thing you can buy or have, it is a series of processes and practices that must be constantly refined. Good cyber hygiene and training are key components of any cybersecurity program, as well as policies and procedures designed to reasonably protect sensitive information. But, beyond that, there is an expectation that any firm will work to identify vulnerabilities within their systems, networks, and infrastructure. Without proper and regular vulnerability assessments, an organization has no way of knowing what risks or threats it may be facing, or where to direct scarce resources. This “first step” or orientation is essential to an adequate security program and is being addressed in different ways by different regulatory bodies. In addition, the identification of vulnerabilities affecting your systems and organization is one of the first items mentioned in the NIST Cybersecurity Framework.[i]
In the last several years, the speak coming from regulators, customers, and vendors has all been centered on cybersecurity: what it is and how to have “good cybersecurity” or how to be “cybersecure”. By this point, we all realize that cybersecurity is not simply a thing you can buy or have, it is a series of processes and practices that must be constantly refined. Good cyber hygiene and training are key components of any cybersecurity program, as well as policies and procedures designed to reasonably protect sensitive information. But, beyond that, there is an expectation that any firm will work to identify vulnerabilities within their systems, networks, and infrastructure. Without proper and regular vulnerability assessments, an organization has no way of knowing what risks or threats it may be facing, or where to direct scarce resources. This “first step” or orientation is essential to an adequate security program and is being addressed in different ways by different regulatory bodies. In addition, the identification of vulnerabilities affecting your systems and organization is one of the first items mentioned in the NIST Cybersecurity Framework.[i]
The Regulatory Overview
SEC – The Securities and Exchange Commission has highlighted vulnerability scanning in all of its recent cybersecurity documentation and releases.
- OCIE’s first Cybersecurity Initiative of April, 2014 questioned if a Firm conducts periodic risk assessments to identify both cybersecurity and physical threats and vulnerabilities.[ii]
- OCIE’s second Sweep of September, 2015, further stated that “examiners may assess whether firms… assessed system vulnerabilities.” The sweep requested “information regarding the firm’s vulnerability scans and any related findings and responsive remediation efforts taken.”[iii]
- The Division of Investment Management suggested that advisers may wish to consider, in the context of their cybersecurity programs, conducting a periodic assessment of “internal and external cybersecurity threats to and vulnerabilities of the firm’s information and technology systems”.[iv]
FINRA – In its Report on Cybersecurity Practices from February 2015, FINRA suggested that effective practices for comprehensive risk assessments include “an assessment of external and internal threats and asset vulnerabilities and prioritized and time-bound recommendations to remediate identified risks.”[v]
CFTC – In October of 2015 the CFTC adopted the NFA’s recommendations regarding Information Systems Security Programs (ISSPs). The ISSP is similar to the “assessments” mentioned by both the SEC and FINRA. Within the ISSP, the NFA expects its members to use a formal process to develop an ISSP that is appropriate to the members business and that includes functions to identify threats and vulnerabilities.[vi]
What is Vulnerability Scanning?
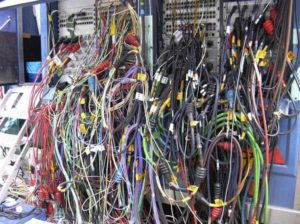
In its most limited sense, vulnerability scanning is identifying weaknesses that may be present on your network. This can be accomplished by any number of software platforms that test for known holes in various pieces of technology. The definition lists are based upon known security problems. The idea behind running regular vulnerability scans across your networks and systems is to identify those pieces of software or hardware with known weaknesses and alerting you. The idea here is that, if the threat has been identified and publicly disclosed, both you and the bad guys know about it.
This threat intelligence is essential. If, however, a vulnerability has been identified in a system or a specific piece of software, hackers around the world will be running scans of all systems that they can locate on the internet, attempting to capitalize on this known weakness. It is important to note that new threats and vulnerabilities are identified on a daily basis.[vii] If your firm runs a single vulnerability scan, it will identify those weaknesses that are present as of that point-in-time. It will not identify weaknesses that are yet to be discovered (Zero Day Threats). In order to remain current, vulnerability scanning should be conducted on a regular basis.
Vulnerability Scanning – Beyond Technology
A scan of identified weaknesses is an essential step for any company that wants to take cybersecurity seriously. However, network and system scanning is just the first step. Consider that vulnerabilities to your business may not come solely from a technology vector, but also from a human one. Regular scans and reporting could suggest a healthy network, but if employees are clicking on links in fraudulent emails or are over-sharing information on social media, you could quickly find yourself under attack from a different and more insidious vector. We encourage you to expand the scope of vulnerability definitions beyond technology. Your reviews should include human weaknesses surrounding email use, internet use, and mobile device use. A comprehensive review should examine social media and your firm’s general web presence. Think like someone who is trying to break into your network. What information is freely available? What kind of a map of your organization could you build just looking at your public website? Are there any articles out there detailing your practices, or statements that your employees may have offered providing clues about how your firm operates, or indeed, where its intellectual property might lay? Does your company maintain a Facebook page or advertise for public meeting and get-togethers? All of these issues and more could represent vulnerabilities to your firm.
Don’t be afraid to identify these vulnerabilities. Indeed, many customers that we work with on this process groan when they discover something uniquely private to the firm being disclosed publicly. But this type of a deep and regular look at your firm and its digital footprint is the only way that you can begin to further secure your organization. Just because you aren’t looking doesn’t mean that the hackers aren’t either. Once you have determined a list of weaknesses and vulnerabilities, technical or otherwise, you can begin to prioritize a remediation list. From the technical side, it is likely that you can fix many of the problems noted in a vulnerability scan. From a human side, you can begin to identify training opportunities and procedural changes that will make your firm more secure today and in the future.
[i]NIST Cybersecurity Framework, Subcategory ID.RA-1: http://www.nist.gov/cyberframework/upload/cybersecurity-framework-021214.pdf
[ii]OCIE’s 2014 Cybersecurity Initiative: https://www.sec.gov/ocie/announcement/Cybersecurity-Risk-Alert–Appendix—4.15.14.pdf
[iii] OCIE’s 2015 Cybersecurity Initiative: https://www.sec.gov/ocie/announcement/ocie-2015-cybersecurity-examination-initiative.pdf
[iv] Division of Investment Management Guidance: https://www.sec.gov/investment/im-guidance-2015-02.pdf
[v] FINRA February 2015 Report on Cybersecurity Practices: https://www.finra.org/sites/default/files/p602363%20Report%20on%20Cybersecurity%20Practices_0.pdf
[vi] NFA Adopts Interpretive Notice Regarding Information Systems Security Programs – Cybersecurity: https://www.nfa.futures.org/news/newsNotice.asp?ArticleID=4649
[vii] The Common Vulnerabilities and Exposures (CVE) List is updated daily. See: https://cve.mitre.org/





